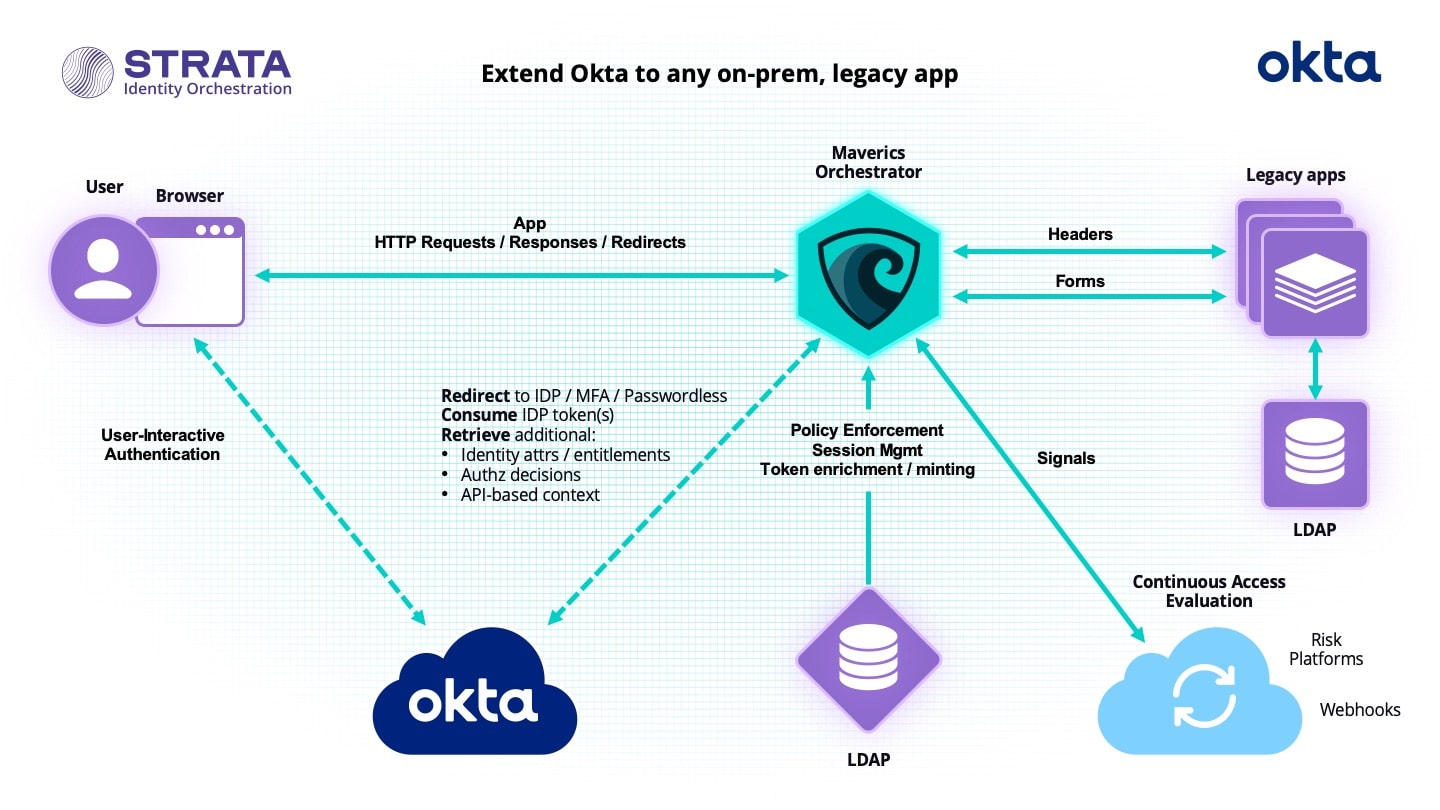
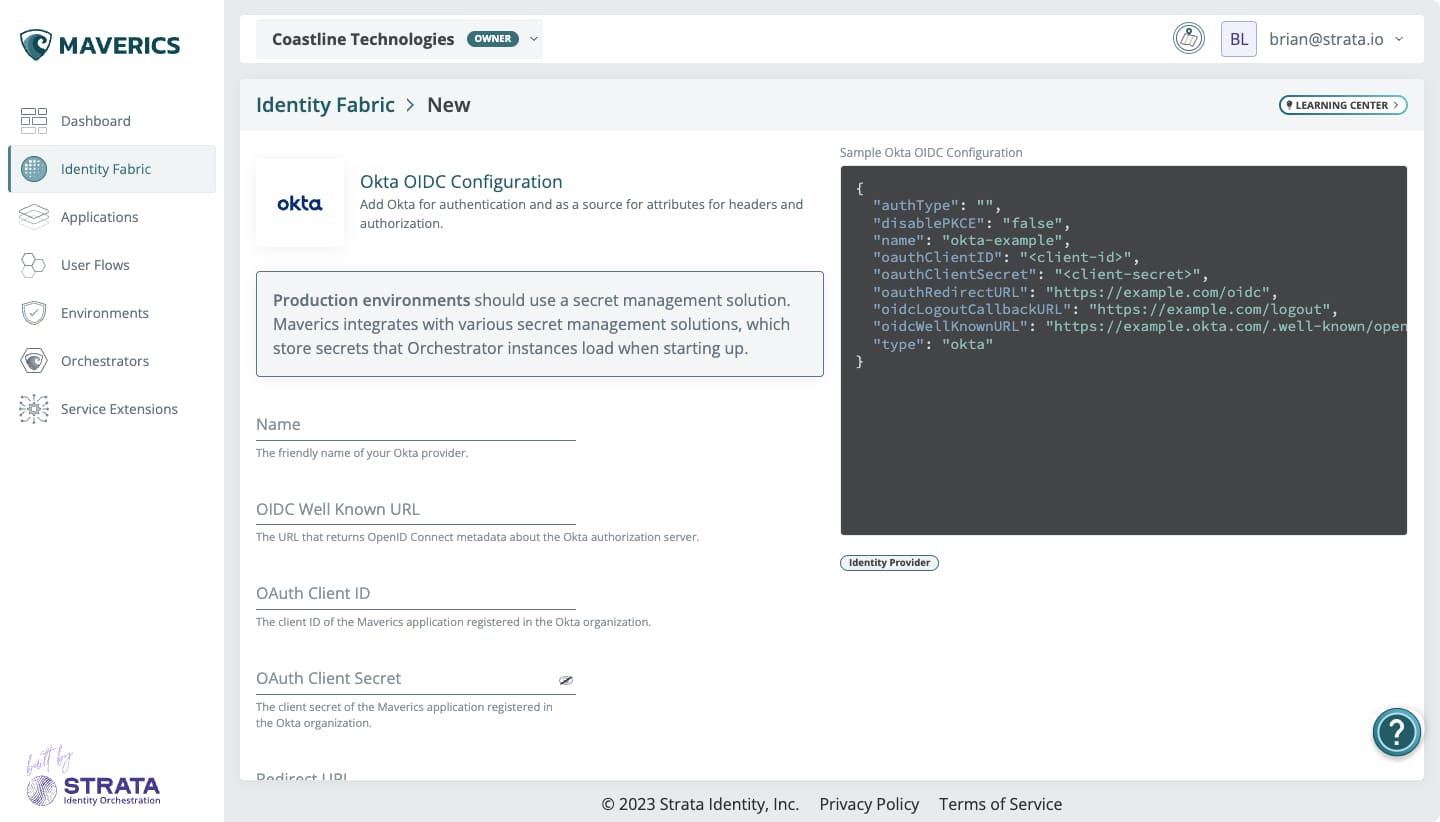
How to extend Okta to any on-prem, legacy app
Deploy Okta and protect headers- and forms-based or LDAP-bound apps without refactoring.
- Extend Okta’s modern authentication and authorization to any legacy app
- Deploy in hours without navigating change management or app downtime
- Protect all apps — no matter where they are — without disrupting the user experience
Solve more modernization challenges with ready-to-deploy recipes

Keep your employee data sovereign, local and resident. Support your multi-national operations with region-specific IDPs that give users controlled access to common apps.

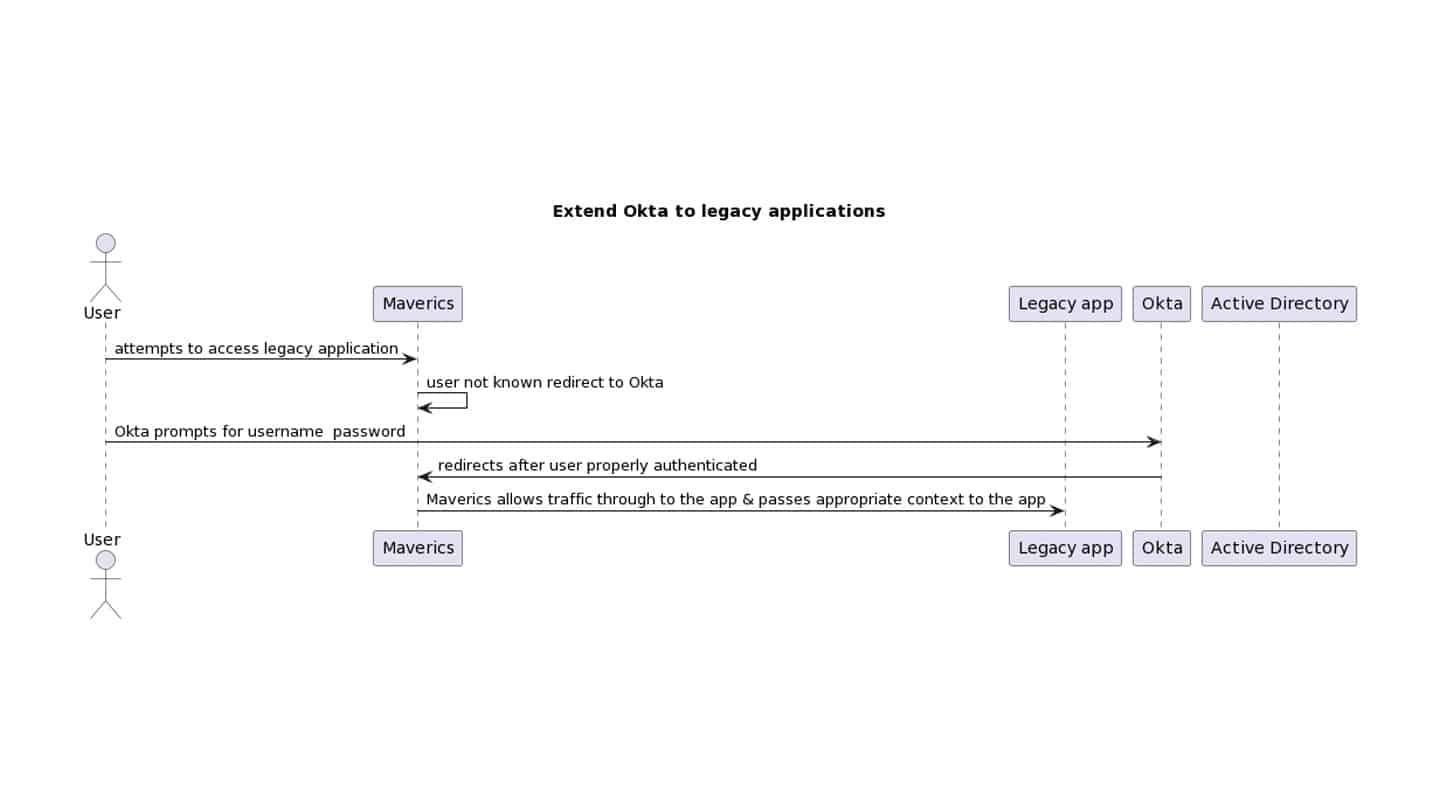
Still using Active Directory to authenticate users? Secure your legacy mission-critical apps with a modern IDP instead — without refactoring.

Break up with your outdated IDP, keep the complex access policies you love, and replace it with modern authentication and passwordless protection from CyberArk Identity — all without rewriting your apps.
Ready to cook up your perfect identity modernization solution?
Stop juggling disparate identity services. Unleash the power of Strata’s orchestration recipes. Whether you’re dealing with legacy app modernization or controlling multi-cloud access, Orchestration Recipes have got you covered.