Identity Orchestration Buyer’s Guide

Identity Orchestration Overview
The move to multi-cloud has forced a fundamental change in how identity is managed across multiple, distributed platforms and identity systems. Identity orchestration is gaining momentum by building a distributed Identity Fabric that enables consistent access and identities across multiple platforms.
Multi-Cloud Identity Use Cases
There are three common use cases that illustrate the need to consider a distributed identity fabric:
1. Multi-cloud environments needing consistent identities and policies
2. Extending on-prem apps and identities to the cloud
3. Modernization – migration from legacy identity to modern identity systems
These uses will be covered in more detail in this guide.
Identity Orchestration Challenges
A number of challenges that are unique to multi-cloud environments must be overcome to achieve successful identity management:
Multi-Cloud Introduces Identity Fragmentation and Silos.
Organizations using more than one cloud must contend with more fragmentation from multiple silos, which makes managing secure access to apps difficult. Organizations need to manage identities and access consistently across platforms, regardless of vendor.
Multi-Cloud Needs Consistent Identities and Policies.
Many organizations run apps on multiple cloud platforms and need to provide consistent access to users regardless of what cloud platform the app runs on. Further, each cloud has a built-in identity system that manages ‘local’ user accounts. These local accounts must be consistent across platforms to support SAML and OIDC-based SSO. Further, access policies on these cloud platforms need to be consistent as well. Without consistent policies, it’s difficult to manage access or demonstrate compliance.
Remote workers require secure access to on-premises apps and data.
Accelerated by mandates to support remote workers, enterprises must quickly adapt to a massive rise in the number of employees working remotely. VPNs can only scale so much and what’s needed is a way to extend access to on-premises apps to cloud-based users. These cloud-based users need secure Zero-Trust architecture and seamless access to apps and data that reside behind the firewall.
App-to-Identity Integration Results in Lock-In.
For the past 10 years, enterprises have deployed identity infrastructure to support on-premises custom web apps. These apps were integrated directly with legacy identity infrastructure. Moving these apps to the cloud means rewriting apps to work with a new identity system, taking months of developer time. Apps that are hard-wired to a single identity vendor leads to more lock-in and limited choices. As a result, organizations are locked into legacy identity platforms, preventing apps from moving to the cloud.
Multi-Cloud Requires a Higher Level of Scale.
Consider managing identity and access for dozens of apps and thousands of identities, now multiplied by the number of cloud platforms in use. Factor in the rapid increase in the number of remote workers that need to access cloud-based apps and it’s simply not possible to keep up with changes using manual effort.
Need Gradual, Agile Migration Capabilities.
Enterprises have significant existing on-premises IT investments used to run the business. Moving these business-critical apps requires working with the dependencies between apps and infrastructure. It’s not possible (or a good idea either) to do ‘big bang’ migrations or modernize everything all at once. What’s needed is an agile approach that supports an app-by-app and user-by-user incremental migration model that decreases risk and accelerates execution.
Need Zero-Trust Secure Architecture.
With cloud deployments, networking plays a different role than on-premises as identity has become the new perimeter. As apps span multiple cloud platforms and on-premises platforms users must cross the open Internet to access them. What’s needed in this case is to assume that all networks are hostile and implement mutual authentication and encryption for all communications. Further, managing access to system-level credentials is critical.
Core Multi-Cloud Identity Use Cases
Multi-cloud platforms are the most common scenario involving two or more cloud platforms. Additionally, the mix of on-prem and public clouds adds new cloud and identity platforms. Some organizations use multiple cloud platforms to avoid vendor lock-in and spread their risk across several cloud vendors to keep their options open. They can also optimize their costs by moving workloads to the best-priced platform at any given time. Other organizations end up with multiple clouds through a merger or acquisition that historically used different technology stacks. And finally, some companies use multi-cloud for high availability and redundancy to dynamically failover to a redundant cloud provider, most likely on a different cloud vendor.
1. Multi-Cloud Identity.
As companies adopt multiple cloud platforms they need consistent access to apps that run across those clouds. Composite apps with composite identity attributes from distributed identity systems also require an identity fabric. The following graphic illustrates the need to have consistent policies and identities across all cloud platforms.
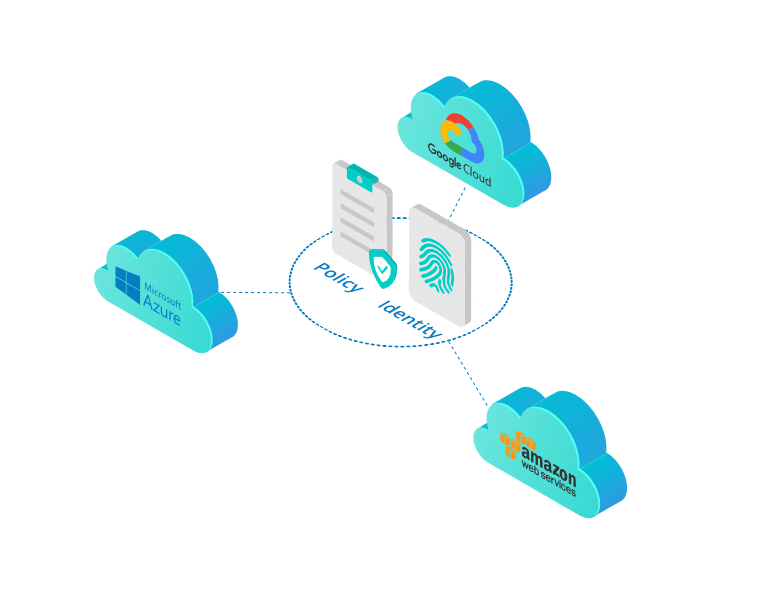
The need to have consistent policies and identities across all cloud platforms.
2. Hybrid Extend Enterprise Apps to Cloud Users.
The second use case requires that access to on-prem web apps be extended to cloud users. When identity policy is managed in the cloud, Single Sign On can be provided from the cloud through a proxy to the on-prem app. Also, maintaining consistency between on-premises and cloud identity is essential for hybrid use cases. The following illustration shows how on-prem apps can be extended to cloud-based users.
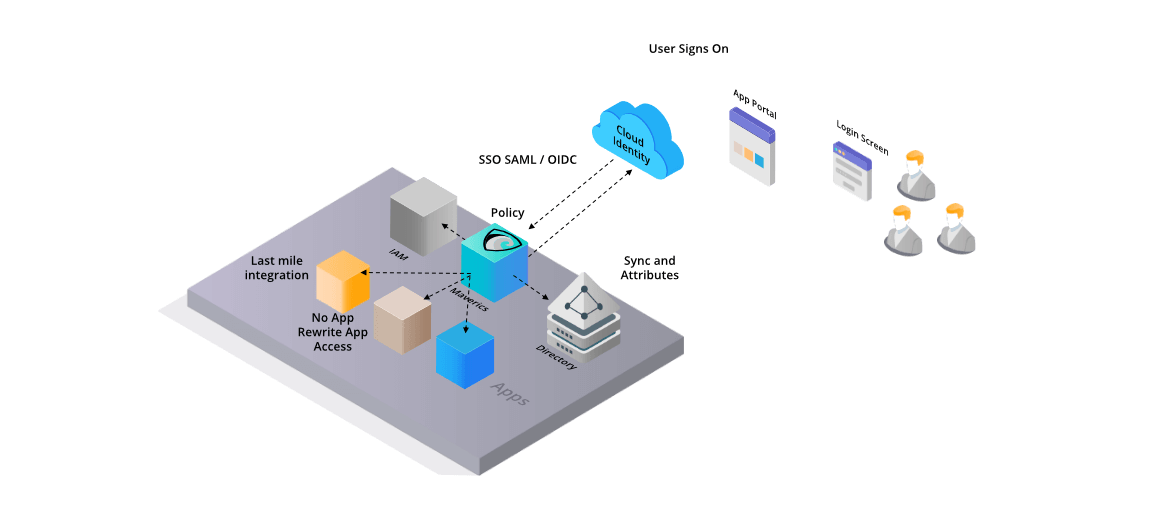
How on-prem apps can be extended to cloud-based users.
3. Migrate from legacy identity to modern identity.
The third identity orchestration use case is providing a solution to migrate legacy identity to modern identity. This requires the discovery of the legacy identities and then a legacy-to-modern live migration coupled with session abstraction. This approach allows you to migrate apps without rewriting them.
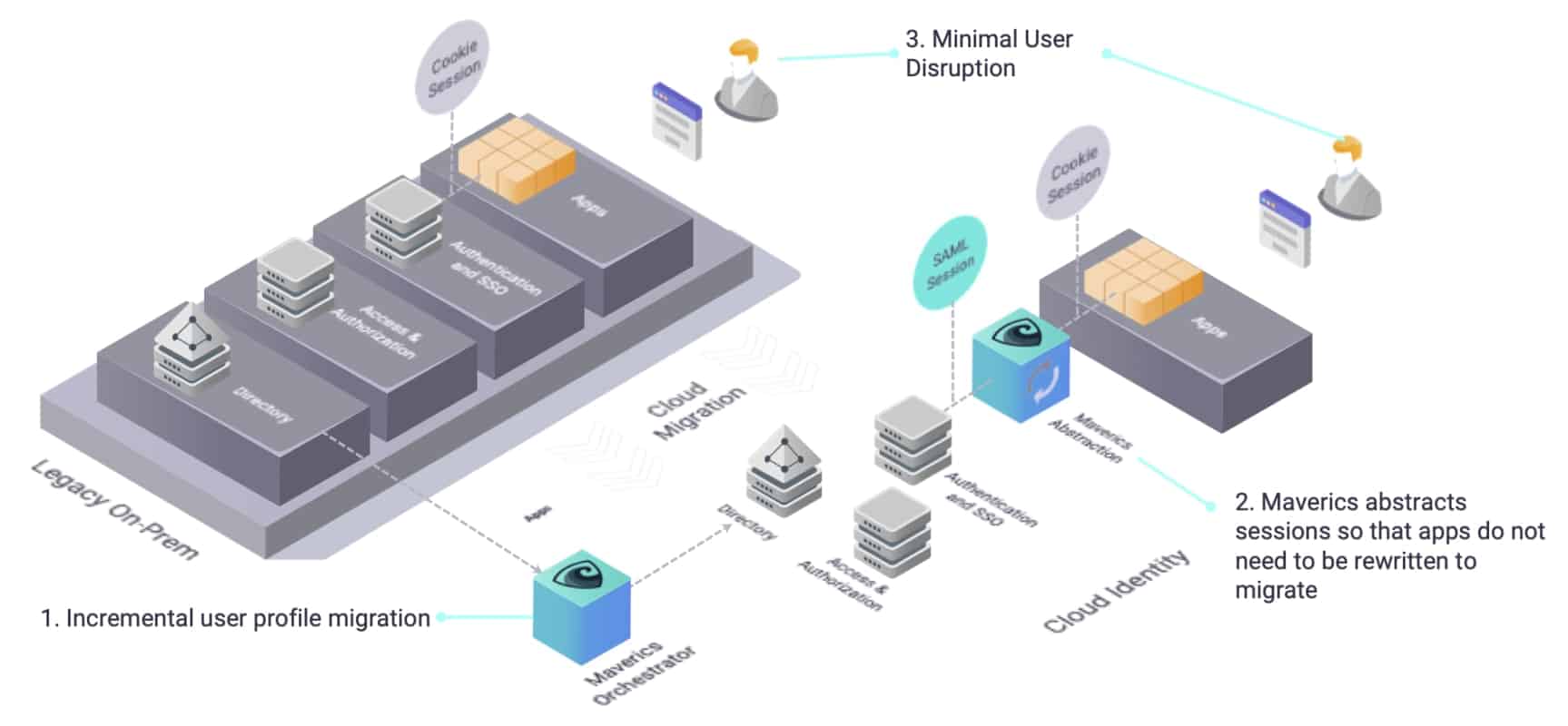
Providing a solution to migrate legacy identity to modern identity.
Modernize any app with any IDP in minutes. Join the 'Orchestration Kitchen' workshops.
Detailed Solution Criteria
Let’s take a closer look at the key criteria that you’ll want to evaluate during your vendor review and product selection.
Multi-Cloud Policy
There are several criteria for cloud policy that are vital to ensure your existing identity policies can be managed across multiple clouds:
Multi-cloud Identities
You’ll also want to evaluate multi-cloud identity support with the following criteria in mind:
Identity Abstraction and Integration
Strata’s Maverics provides an abstraction and integration layer that facilitates the three main use cases discussed earlier.
Enterprise-Grade Capabilities
Architecture
Ease of Implementation
Pricing and ROI Justification
Identity Orchestration Buyer’s Guide Conclusion
The adoption of multi-cloud platforms has created numerous challenges to securely manage identities and policies. Nearly every company that has adopted the cloud still has legacy applications that run behind their firewall. Each cloud provider has created silos of identities that must be managed separately with a greater cost of time and expense.
These three use cases are the key identity challenges faced by organizations today. Multi-cloud environments require consistent identities. Extending on-prem apps and identities to the cloud is also required so that users can securely access legacy applications. Modernization of identities includes the migration from legacy identity to modern identity systems.
The solution to these challenges is to use a natively distributed architecture in an enterprise-ready way, with easy implementation and strong ROI. Strata’s Maverics Platform™ solves these key areas of identity: managing multi-cloud identities, extending access to on-prem apps, and migrating legacy identity. To see how, please request your own demo at strata.io/demo.