Rise of the identity domains (identity silos)
How hybrid IT infrastructures will soon push IAM to the brink.
What are identity silos?
Identity domains, also known as identity silos, are when user identities live in different interoperable systems that can’t communicate with each other.
Once upon a time, an enterprise’s infrastructure lived in a fortress. Tightly contained within the strong walls, it was secure. Then came the cloud and SaaS, and everything changed. The apps that lived in the Cloud were cool and modern and could do things that the ones on-premises could only dream of. The cloud enabled organizations to move faster, be agile, and empowered a remote workforce.
Organizations still needed their on-premises systems, which created the hybrid world of two systems: cloud and on-prem. With the hybrid IT infrastructures came the rise of Identity domains.
What is a hybrid cloud?
A hybrid cloud is a cloud computing environment that uses a mix of on-premises, private cloud, and third-party public cloud services with some sort of orchestration between the two platforms.
Forrester estimates that the hybrid cloud market will reach $411 billion by 2022. According to the RightScale 2019 State of the Cloud Report, Enterprises with a hybrid strategy (combining public and private clouds) grew to 58 percent in 2019 from 51 percent in 2018. A host of other challenges have opened up as the hybrid cloud approach explodes, with 66 percent of enterprises already having a central cloud team or center of excellence, with another 21 percent planning one (up from 57 percent and 24 percent the previous year) to manage cloud governance.
The cloud dichotomy: IT infrastructures simplified and became more complex
During the rise of cloud computing, we still deployed lots of on-premises Identity Access Management (IAM) software because IAM was the only option at the time. Some departments within organizations began to experiment with public cloud infrastructure and Software as a Service (SaaS). Each new cloud platform brought its own built-in identity management systems.
We all knew this out-of-band experimentation might cause problems down the road, but we were all busy and decided to worry about it later. We tried to apply some band-aids such as using virtual directories for our AD forests, federation and SSO to build some bridges between on-premise and cloud and other stuff.
However, these solutions worked against us because they made it seem like the problems were solved when they really weren’t. Communicating the nuance of what was wrong to our CIO was nearly impossible. Everything seemed to be working fine from a 10,000-foot view.
Identity domains become the new identity silos
You’ve heard the saying that too much of a good thing may not be so good? Before the proliferation of public clouds and hybrid clouds, identity domains were purpose-built for a particular set of applications. Life was good because identities were centralized and lived behind a company’s firewall. But the hybrid cloud and the need for hybrid identity management changed all that. Identities started to become much more distributed along with the technology to manage them. Soon, the experimentation with these new clouds (AWS, Azure, Google, etc.) platforms transitioned to production deployments, and the use of each cloud-native identity system expanded and hardened to meet those production requirements. The reliance on each cloud platform’s native identity stack increased. Which meant organizations found themselves locked in.
In short, that’s how identity domains have become the new silos. Almost overnight, identities, policies, and configurations have proliferated and cannot easily be moved to a different platform. You cannot centralize your identity management and without centralization, visibility and control becomes lost. You end up straddling the legacy and cloud application world of identities. The old identity systems are unable to adapt. The new systems aren’t built to accommodate heterogeneity. The identity model is effectively broken in two.
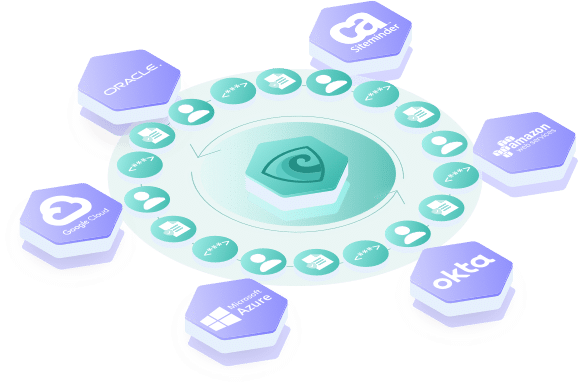
A better way to do app & identity migrations using an Identity Fabric
Albert Einstein once said, “In the middle of difficulty lies opportunity”. There is a solution to this vexing identity challenge, and it lies in something known as an Identity Fabric. Understanding this approach, it helps to flip our viewpoint of identity and access management on its head. Instead of approaching the identity challenge from the infrastructure angle, think about the apps angle instead. With the proliferation of identity domains, there’s no easy choice to standardize on one single identity system.
You might think that the only solution is to unwire an app from its legacy identity domain and wire it to a new, modern cloud identity domain. But this repeats the lock-in of the past and is costly and time-consuming. There must be a better way. This is where the identity fabric comes into play. The Identity Fabric can talk to ANY identity domain, giving your apps the flexibility to be moved anywhere and integrated with any platform’s identity domain without rewriting the app!
Hybrid IT infrastructures and identity silos
While hybrid infrastructure is here to stay, it has fundamentally broken the identity model. Legacy identity systems don’t talk to cloud platform identity systems and vice versa. Simply wiring an app to a cloud platform’s identity isn’t a good solution because the app must be rewritten at great expense and time. That’s where an Identity Fabric comes in.
Using an identity fabric has serious benefits:
- Take advantage of the distributed nature of hybrid.
- Enjoy choice and flexibility when moving from the old to the new.
- Chose if you need to rewrite apps or not.
The identity fabric offers the best of both worlds and gives organizations a true solution that isn’t a short-term fix. Don’t wait for your IAM to be pushed to the brink before exploring a better way with the identity fabric. Message us with your biggest IAM challenges today. If you’re ready to start to think about your multi-cloud identity strategy, download the identity fabric datasheet or get in touch and we can show you how it works in your environment.