How to add HYPR step-up authentication
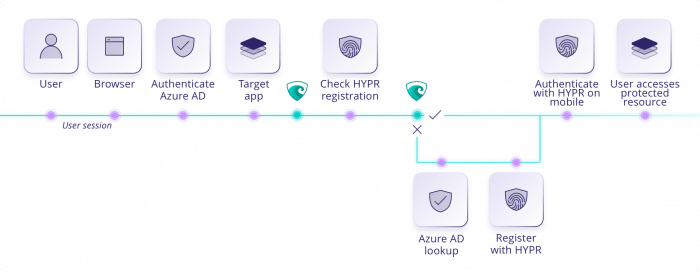
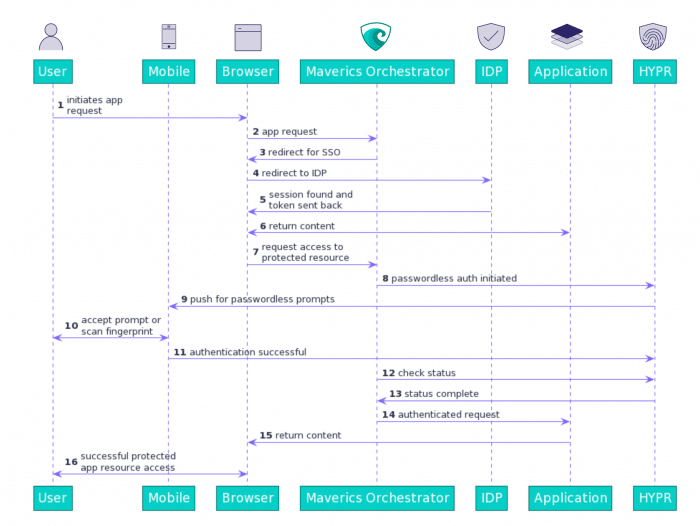
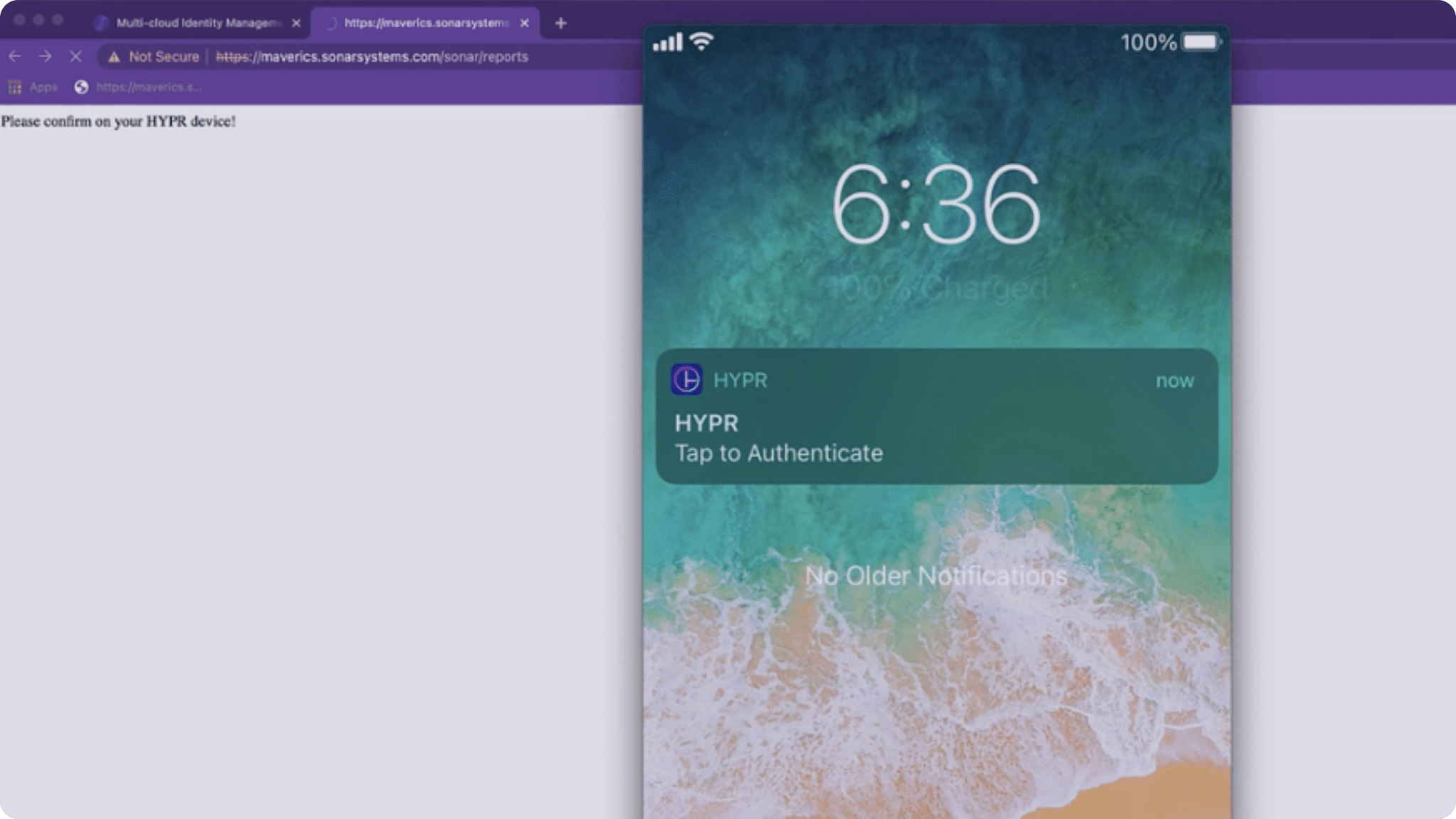
Leverage AzureAD as your cloud identity target and add HYPR step-up authentication protection to a protected resource in any app without rewriting the app itself.
- Quickly deploy HYPR step-up authentication to any protected resource or data
- No custom code or app rewrites are required to add HYPR step-up authentication
- Phased deployment reduces risk and supports coexistence of authentication solutions
- Reduce friction by enrolling users to HYPR within existing authentication flows
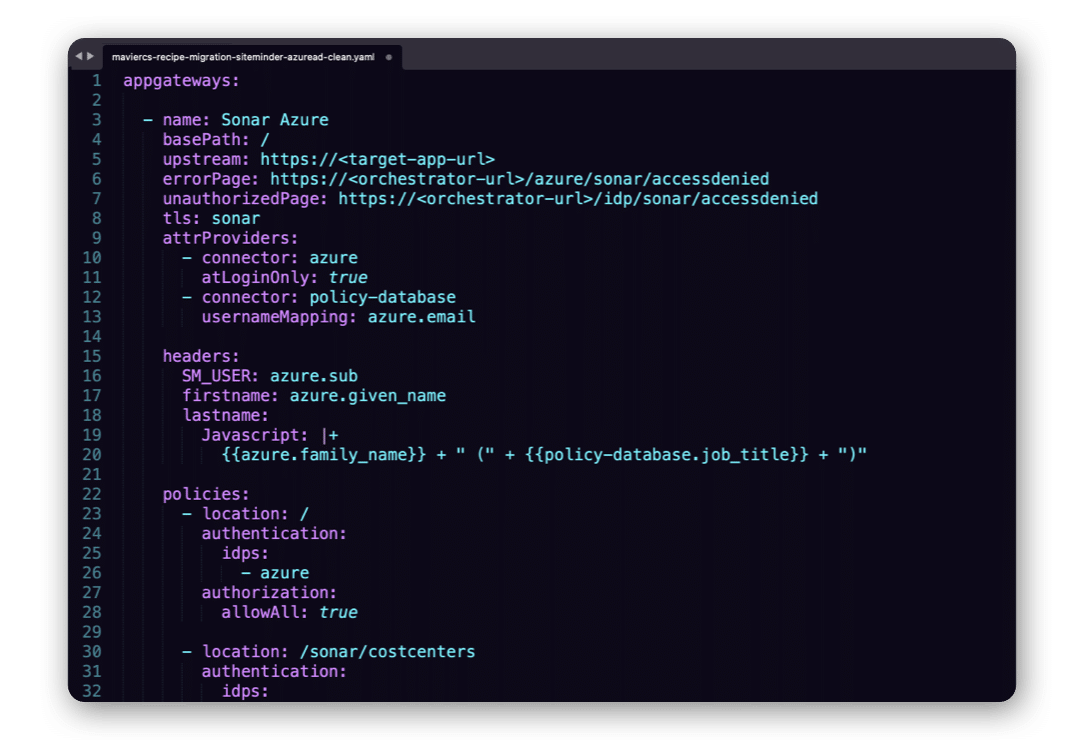
Get your YAML config settings and deploy
Maverics Identity Orchestration works as a simple YAML config: just fill in the blanks and go. There’s no custom code, no rewrites and no long engagements. You may need to make light config adjustments based on your environment, but that’s it.
Ready to leave this particular legacy in the past? Grab this recipe and modernize.
Solve more modernization challenges with ready-to-deploy recipes

Keep your employee data sovereign, local and resident. Support your multi-national operations with region-specific IDPs that give users controlled access to common apps.

Still using Active Directory to authenticate users? Secure your legacy mission-critical apps with a modern IDP instead — without refactoring.

Break up with your outdated IDP, keep the complex access policies you love, and replace it with modern authentication and passwordless protection from CyberArk Identity — all without rewriting your apps.
Ready to cook up your perfect identity modernization solution?
Stop juggling disparate identity services. Unleash the power of Strata’s orchestration recipes. Whether you’re dealing with legacy app modernization or controlling multi-cloud access, Orchestration Recipes have got you covered.