RECIPES › CLAIMS TRANSFORMATION
Claims Transformation for SAML and OIDC
No need to rewrite applications in order for them to accept different identity protocols
Future-proof applications in case you change SAML or OIDC providers at a later time
Allow for the addition of additional modern authentication solutions within the existing UX
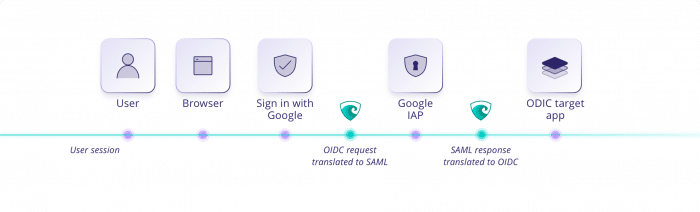
Recipe summary: Claims Transformation – SAML and OIDC
This recipe demonstrates how Maverics makes it easy to incorporate SAML and OIDC to sessions and apps by abstracting the complexity of SAML or OIDC. With Maverics, you can add SAML and OIDC to apps without rewriting them. Maverics converts SAML and OIDC claims into HTTP headers that drop right into your apps. This enables applications that expect OIDC to accept SAML attributes without any need to refactor the apps themselves.
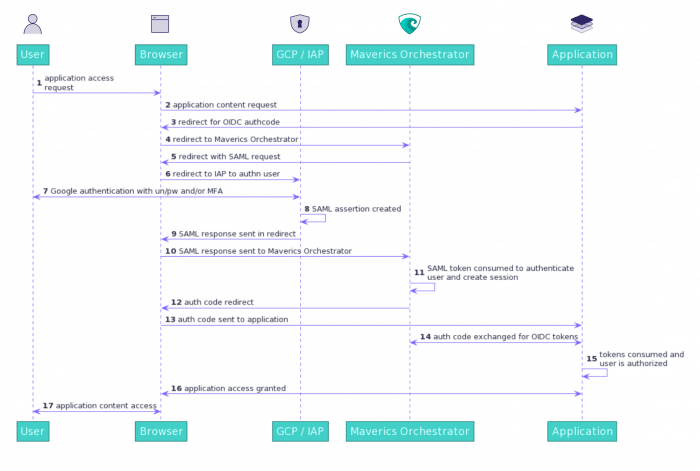
Recipe instructions: Claims Transformation – SAML and OIDC
Recipe sequence diagram: Claims Transformation — SAML and OIDC
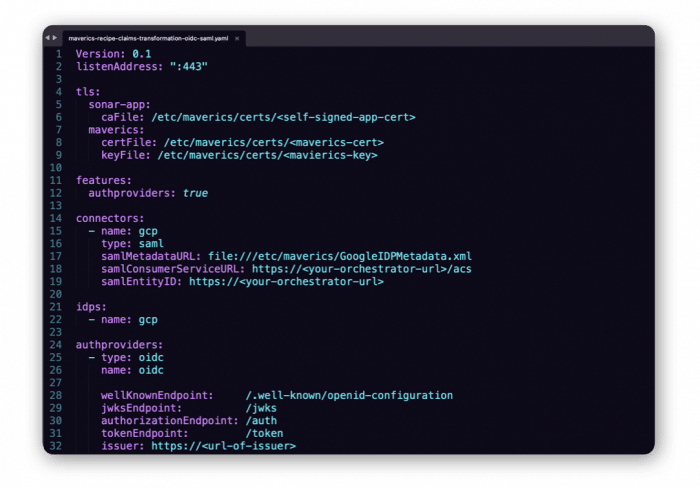
Recipe YAML config settings: Claims Transformation — SAML and OIDC
Maverics Identity Orchestration works with a simple YAML config* (as shown in the figure to the right). No app rewrites or custom code is required. Download this recipe’s full config file below.
*Config may vary based on your environment.